Introduction
Cerious Cybernetics Corp. is a sectored cybernetics research and development company, mainly located in London, UK, with a team of 60 full-time employees at its centre and all other accessory personnel. Contract new technological research & development contracts with the UK Ministry of Defence and the United States Department of Defense, and the security of its information and assets becomes even more significant since they have to operate in an environment full of risks (Ademola, 2021). Cerious Cybernetics Corporation, being aware that cyber threats are always finding new ways, is taking measures to build timely and relevant information assurance and risk management policies quickly. This paper will analyze the principles of information assurance and risk management and their implementation, envision present scenarios, develop strategies for future situation improvement plans (SIPs), and competently reduce ransomware threats. Therefore, the analysis of Cerious Cybernetics Corp. is the major driver for risk mitigation, ensuring that any threats and the company’s operations are secured.
Understanding Information Assurance and Risk Management
Overview of Information Assurance and Risk Management Principles
Information assurance and risk management form the basics of the modern cyber security structure that aims to protect the information asset values and ensure the continued operations of businesses in the face of the evolving cyber threat revolution. Information assurance means security policies, procedures, and technologies that draw upon to protect and efficiently maintain the accuracy of sensitive data (Alshurideh et al., 2023). This refers to protecting the privacy of information while at the same time making sure data is intact and available to authorized persons only to curb the risks entailed by cyber threats such as data breaches and data loss. The fundamental concepts of information security consist of confidentiality, which aims at restricting access to information of a sensitive nature and to accredited individuals only; integrity that ensures data retains its accuracy and is undamaged; and availability, which promises the availability of data as a service when needed (Nifakos et al., 2021).
Figure 1: Principles of Information Security and Assurance
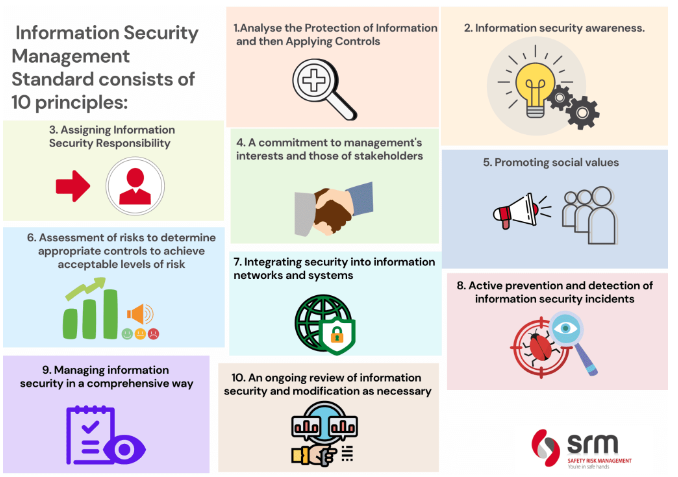
Source: (Alshurideh et al., 2023)
Conversely, risk management is a controlled process of discovering, examining, and limiting an organization’s risks. The key risks are related to information assets and the critical thrust of the organization. It holds the task of spotting the possible risks and vulnerabilities, assessing the potential impact that could be caused on the business operations, and identifying the risk mitigation measures to avoid or reduce identified risks (Alshurideh et al., 2023). Risk management strives to balance exploiting opportunities fully and making provisions for detrimental effects by directing efforts to reduce risks if they are high probability and high severity.
Competent influence and risk management methods of information assurance can only be implemented with a multidisciplinary view, starting with technical, management, organizational, and legal aspects. It consists of determining security targets (the level of protection required to achieve business objectives) and selecting security controls (measures) to meet business goals, regulatory requirements, and industry standards (Nifakos et al., 2021). Similarly, regular information assurance and risk management procedures should be monitored continually, analyzed, and revised to consider rapidly evolving threats and the business environment.
Importance of Information Assurance and Risk Management in Modern Organizations
In the rapidly evolving landscape of modern organizations, information assurance and risk management have become increasingly indispensable, especially within cybersecurity. Several key points underscore their paramount importance in ensuring the resilience and viability of organizations in today’s digital era:
Protection of Sensitive Data: Amid the digitization trend and with all that business crucial data being produced and processed by digital technologies, organizations obtain and handle large amounts of sensitive data. This includes this company’s patented information, financial figures, customer information, and patents (Stoneburner, Goguen, and Feringa, 2022). Proper information assurance procedures are critical in securing long-term privacy interests by preventing unlawful access, editing, or stealing. When data compromise and virtual aggressions are typically present, organizations must safeguard vital data to preserve stakeholders’ trust and conformity to regulatory requirements such as GDPR and HIPAA.
Preservation of Business Continuity: Information assurance and risk management are key components in business continuity efforts, particularly during cybercrimes and other disruptions. Information loss and data breaches due to cyber-attacks like ransomware, DDoS attacks, and malware infections can weaken an organization’s system and infrastructure, increasing financial woes and causing reputation collapse (Kandasamy et al., 2020). Adopting robust risk management measures and thinking through contingency action plans would ensure that organizations moderately handle such incidents and sustain the delivery of vital services, preventing business interruption.
Protection Against Financial Losses: The repercussions of cybersecurity incidents may bring devastating economic effects to organizations because they involve direct proceeds and costs such as compensations and penalties, legal bills, and restoration charges. Aside from the indirect costs related to reputation loss, market share erosion, and decreased customer trust, these can also negatively impact any company’s financial position (Stoneburner, Goguen, and Feringa, 2022). The right information protection and risk management systems building require organizations to determine specific threats and economic risks and prevent them from keeping their region stable and sustainable.
Compliance with Regulatory Requirements: With the increasing regulatory environment, organizations must meet a pool of legal and regulatory compliance for data protection and security across various lines. Exceeding these regulations can bring many penalties or sanctions, such as being fined or blocked (Kandasamy et al., 2020). The organization’s reputation is also going to be damaged. Information assurance and risk management take an important role in compliance with all related regulations by adopting adequate controls, holding regular audits, and keeping documents that show evidence of the necessary adherence to the provisions of the law.
Protection of Intellectual Property and Competitive Advantage: Intellectual property (IP) is a crucial asset to many companies, and it can sustain a market advantage and a generator that enables creation and development (Stoneburner, Goguen, and Feringa, 2022). The information assurance measures in which IP or intellectual properties are protected against IP theft, espionage, or unauthorized disclosures are of utmost importance. By preserving the intellectual property space, organizations can protect their market leadership, maintain a competitive advantage, and gain long-term industry performance.
Analysis of Current State Cerious Cybernetics Corp.
Overview of Cerious Cybernetics Corp.’s Current Information Assurance and Risk Management Practices
Cerious Cybernetics Corp. is currently operating under a multisided conduit of information assurance and risk management, in which success is guaranteed by the robustness of its critical assets and seamless flow of operations. The company has implemented strong policies, procedures, and safeguards that safeguard sensitive data from possible threats, mitigate any breach of requirements, and maintain compliance (Ademola, 2021). Access controls, which include identifying users through authentication and limiting permission using role-based access controls to the highest levels of privacy, have become one of the biggest diagnostic tasks of information security professionals. Finally, security standards implemented by Cerious Cybernetics Corp. involve implementing encryption techniques to secure data during both transferring and storage and offer some levels of protection against interception or disclosure by unauthorized persons, especially where remote access can be provided and mobile devices utilized.
Moreover, the technical controls and the organization implement advanced incident response preparedness, maintaining a plan of action that allows the workforce to navigate through detection, analysis, containment, and recovery from cyber-security incidents promptly. Employee training and awareness programs could be the cornerstone of a fast-paced culture of cybersecurity within the organization (Ademola, 2021). It is intended not only to teach staff to identify threats but also to deal with them effectively. The company is reinforced against social engineering risks such as phishing attempts and other human-dependent cybersecurity threats by training and retraining the humans working for the Curious Corp. of Cybernetics.
SWOT Analysis for Cerious Cybernetics Corp.
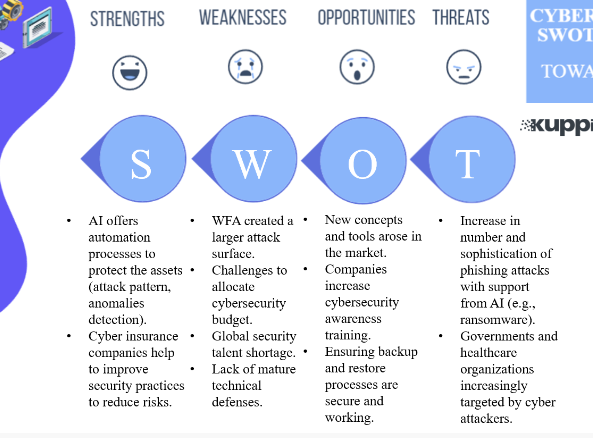
Figure 2: SWOT Analysis of Cerious Cybernetics Corp.
Source: (Engelbrecht, Lindeman and Hoermann, 2019)
Strengths
Cerious Cybernetics Corp., a well-known brand, prides itself on comprehensive security policies and procedures for information security management, providing a robust framework for addressing such security risk challenges. With a team of experienced cybersecurity experts, the organization has a broad disposition ready to implement and maintain all security-related activities (Engelbrecht, Lindeman and Hoermann, 2019). Alongside this, Cerious Cybernetics Corporation works in strategic partnerships with the home and US Ministries of Defense, overcoming obstacles of access to valuable info and technology and gaining insights into new trends and best practices.
Weaknesses
While Cerious Cybernetics Corp. has its positive points, the story may flow unpleasantly when it comes to the complete risk analysis, giving space to potential disruptions in the cybersecurity barriers. Resource constraints, such as the command of limited funds and a limited number of staff, greatly affect the sustainability of investing in security measures (Engelbrecht, Lindeman and Hoermann, 2019). The reliance on technological remedies alone could overlook the risks based on human cybersecurity manifestation, which may be the main vulnerabilities.
Opportunities
The Cerious Cybernetics Corp may avail the possibilities to make enhancements in cybersecurity through collaboration with like-minded agencies that are cybersecurity firms, researching institutions and the government. These networks will take the organization’s features to a new level and open doors to recent technologies and intelligence. In addition, taking on the emerging markets space is a major growth opportunity channeled into exploring the innovations needed to tackle new threats and needs worldwide. Pouring more resources into the innovation of technologies such as AI and ML will improve the organization’s security abilities in the cybersecurity landscape.
Threats
While they address the issue through an active approach, Cybernetics Corp. Cerious Cybercorp. ought to remain constant to fight against potential security problems, including infection with malware, phishing attacks, ransomware, and insider threats. Such strikes may halt operations, reveal confidential information, and harm the authority by making the organization look unreliable (Engelbrecht, Lindeman and Hoermann, 2019). Besides digital privacy, managing complicated regulatory requirements and compliance mandates, including where GDPR and HIPAA laws are concerned, and dealing with the legal and financial consequences of an organization jeopardizing its reputation may also pose a risk. Furthermore, using many outside organizations and providers makes the business depend on vendors and suppliers. It heightens supply chain risks such as vendor breaches and supply chain attacks, which may be severe for business continuity and resilience.
Information Security and Risk Management Practices
The holistic approach of Cerious Cybernetics Corp. includes information security and risk management solutions to counter threats and save many critical assets. The organization utilizes a multi-faceted approach, fusing technical barriers and organizational policies and training employees on diverse cyber-security risks to successfully overcome all threats (Brunner et al., 2020). Access controls thereby encompass a critical function, and their performance lies in user identity verification mechanisms and role-based authorization. Furthermore, Cerious Cybernetics Corp. first prioritizes encryption types to ensure that data in transit can have secure communication and also at rest untouched by unauthorized third parties, particularly remote access or mobile devices.
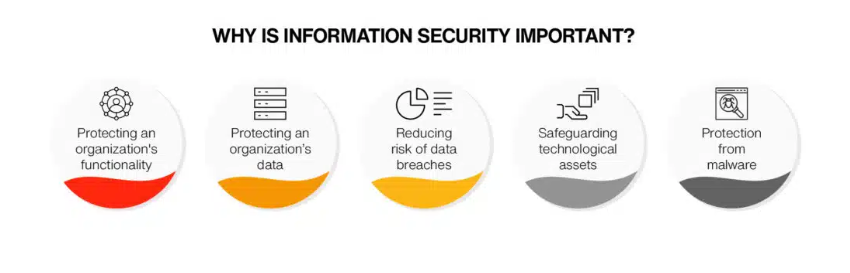
Figure 3: Importance of Information Assurance
Source: (Brunner et al., 2020)
That structure generally has an established emergency response plan to identify, analyze, and isolate cybersecurity incidents promptly. Information security in Cerious Cybernetics Corp. is part of the recruitment process, which involves employee training and awareness programs that empower the staff to carry out their duties effectively (Brunner et al., 2020). Through this investment, the company reinforces its cybersecurity defenses, and the message that it is determined to sustain a safe and reliable operational realm is delivered to the relevant parties.
Recommendations and Solutions
Proposals for Fit-For-Purpose Information Assurance and Risk Management Policies, Procedures, and Practices
To address Cerious Cybernetics Corp.’s information assurance and risk management needs, the following tailored recommendations are proposed:
Comprehensive Information Security Policy: Cerious Cybernetics Corp. would be better off with an all-inclusive data protection policy that addresses issues such as information security and access control and cyber-security measures (Boyens, 2022). To implement this policy, its clearly defined instructions should touch upon data classification, encryption protocols, and access management procedures. Audits and reviews should be conducted regularly to ensure our policies and industry standards are fully compliant.
Risk Assessment and Management Framework: Risk assessment and management frameworks are robust and are the basic point, and this can only be achieved by finding, assessing, and addressing risks most effectively. Curious Cybernetics Corp. must develop an overall strategy for identifying risks at the company level, and the first step is to analyze various stakeholders, such as technological vulnerabilities, regulatory framework, and third-party dependencies (Boyens, 2022). An efficient structure should iron out security procedures, like risk assessment, vulnerability testing, and prioritizing potential threats.
Incident Response Plan: More than anything else, it is necessary to prepare a detailed plan covering all aspects of the incident response process to mitigate or prevent any impact of the security incidents and ensure a timely recovery. To cover cybersecurity matters, Serious Cybernetics Corp. should prepare a detailed road map, including the roles, responsibilities, and procedures for the company branches on how to react to cybersecurity incidents such as data breaches, malware infections, and DoS attacks during the time of business operations (Boyens, 2022). At regular intervals, exercises and simulations should be held to stress the plan and check the organization’s readiness level.
Employee Training and Awareness Programs: Investment in developing employees’ skills and holding awareness programs are the main pillars of building a security-conscious culture among employees. Cerious Cybernetics Corp. will assure structured training courses which involves cybersecurity practices, phishing attacks, and social engineering methods. Before the initial phase of implementation, employees should be adequately informed of the role they will be playing in the process of preserving sensitive information and reporting security incidents that could be observed on time.
Continuous Monitoring and Improvement: Reinforcing a reliable continuous monitoring process is critical for staying ahead of the Malaysian cybersecurity dynamics and taking into consideration Cerious Cybernetics Corp., which will require active monitoring security tools and technologies that will be able to react to incidents that occur in real-time (Boyens, 2022). Auditing procedures should be carried out regularly, and assessments and reviews should be conducted to detect vulnerabilities and build good resilience for security purposes. Another suggested measure is the inclusion of feedback mechanisms to gather input from stakeholders and update the security measures following stakeholders’ feedback.
Discussion Of Recommended Policies, Procedures, And Practices Tailored To Cerious Cybernetics Corp.
Tailoring information assurance and risk management policies, procedures, and practices to reflect the specific necessities of Cerious Cybernetics Corp. requires a sophisticated approach that considers the company’s industry, size, operation conditions, and regular environments.
Data Governance and Protection Policies: Cerious Cybernetics Corp. is heavily concerned with R&D, especially defense contracts; proper data management and protection may be the only choice. Policies should state how to assign the data to the classes (contextual data, auditing information, confidentiality, etc.) and implement encryption (for data in transit and when gathered) (Mishra et al., 2022). In addition, these policies should regulate access control that should be limited only to authorized users. Moreover, measures should be adopted to ensure regular data backups and safety and responsible utilization of obsolete data to avoid data leaks and stay within the framework of data protection legislation.
Cybersecurity Measures and Controls: The Cerious Cybernetics Corp should implement a multi-level cyber security approach to protect its IT infrastructure and intellectual property. It will also use this strategy, which will include the application of firewalls, intrusion detection systems, and endpoint protection solutions to detect and avoid cyber threats (Mishra et al., 2022). Periodic security reviews and vulnerability audits need to be run to identify any network weaknesses and take effective mitigating measures. Additionally, patch management, software updating, and configuration hardening procedures must be implemented to prevent any potential exploitation by cyber intruders.
Incident Response and Business Continuity Plans: The organization’s security depends on developing solid incident response and business continuity plans. They must be created so that the impact of cybersecurity events is minimized, as well as the organization’s stability. Cerius Cybernetics Corp. should highlight, identify, contain, and respond to procedures for cyber security incidents that happen to be ransomware infections. This necessitates setting the jobs and responsibilities, preparing the communication channels with stakeholders, and periodically (once in a while) holding drills and simulations to have a true picture of the plan’s effectiveness. Moreover, restoring critical systems and data within the right period is also a must, keeping in mind that this diverse action will minimize downtime and help control the losses of funds.
Regulatory Compliance and Risk Management Framework: The Cerius Cybernetics Corp. operations must comply with all rules and criteria that guide the industry for data protection and cybersecurity frameworks. They must also adhere to these standards and respect the Personal Data Protection Regulation (GDPR), ISO 27001, and the NIST Cybersecurity Framework (Mishra et al., 2022). The organization must set up a risk management framework that includes risk assessment, measures of mitigation, and checking systems within the risk framework. Establishing periodic risk assessment regulations, evaluating the effectiveness of security measures, and correcting anything necessary to withstand new threats and vulnerabilities are required.
Sample Service Improvement Plan (SIP)
To mitigate and contain the increasing danger of ransomware, Serious Cybernetics Corp. has to implement an SIP about the prerequisite IT security, technological infrastructure, and data protection. This SIP intends to solve the platform attacks with ransomware, thereby protecting its important resources and services from damage.
Enhancing IT Security, Infrastructure, and Data Protection
Several strategic measures need to be taken to strengthen Cerious Cybernetics Corp. against the challenge of ransomware. The organization is to be given an audit to detect all the possible entry points without the correct security measures and how to strengthen the existing infrastructure, which ransomware attacks can exploit. It should encompass the performance of the existing security controls, network architecture, and employees’ practices to provide step-by-step recommendations (Apirion, 2023). Afterward, Serious Cybernetics Corp. should put a defense strategy with multiple layers, consisting of sophisticated endpoint protection software, municipal email filtering, and network segmentation protocols. All system types should periodically be updated and patched to fix known weak points that ransomware threats may target. These steps will reduce the probability of exploitation by ransomware.
However, this should be complemented by a rigorous staff training and awareness program to enlighten them on the dangers associated with ransomware and how they are expected to conduct themselves according to security standards. The level of education includes programs such as awareness-raise lessons about phishing attacks, social engineering techniques, and suspicious email attachments. With Cerious Cybernetics Corp. nurturing a security-conscious posture from its professionals, the personnel can promptly notice and report security incidents (Apirion, 2023).
Risk Assessment, Mitigation Strategies, and Resource Allocation
Combined with building more secure IT controls, Serious Cybernetics Corp. needs to develop comprehensive risk management scenarios and adapt them to the cyber security threat landscape. This includes having risk-based protective measures in a place that could involve the systems and assets that are essential for protection (Apirion, 2023). Proactive monitoring and detection mechanisms and responding to situations are also in place. In case of a ransomware attack, Cerious Cybernetics Corp. should have a prior defined set of rules for changing the connection, halting the virus propagation, and initiating a recovery process.
The resource allocation process is a key position in developing effective ransomware prevention strategies. Cerious Cybernetics Corp. should uphold the provision of adequate resources, either financial or workforce to address the key issues regarding security measures. In this regard, investments in modern security tools, hiring competent cybersecurity personnel, and periodic security audits and checks to evaluate the efficacy of issued controls should be addressed. By implementing these steps into its Service Improvement Plan, Serious Cybernetics Corp. will further strengthen its capacity to resist the impact of ransomware attacks, minimize both the consequences of and the recovery from security incidents, and create an environment that remains operable. Activity and vigilance are the keywords in this case that will ensure proper cyber security of the organization and adapt and evolve the strategies to address newer criminal tactics in the 21st century.
Future Provisions and Considerations
Along with Curious Cybernetics Corp, which is operating in a world with ever-changing cyber safety and technical advances, it will be necessary to have some proactive approaches directed at its security and risk management initiatives for the future.
Adapting to Evolving Cyber Threats and Technological Advancements
Serious Cybernetics Corp. should offer a dynamic approach that stresses agility, innovation, and cooperation to deal successfully in a cybernetic environment where challenges are growing deeper. This involves continuously tracking new cyber threat data, patterns, and modes of exploitation coming out of the industry by attending cybersecurity forums and reading cybersecurity blog posts (Boyens, 2022). Besides, as an investment area, the organization should concentrate on the most recent, effective technologies and solutions that will treble its capacity to defend itself from cyber attacks and secure enhanced resilience. It is not only about using AI, ML, and predictive analytics to reinforce intruder detection but also automating incident response and predicting possible vulnerabilities before they can be attacked (O’Donnell and Gupta, 2023).
Moreover, Cerious Cybernetics Corp. must also develop strategic partnerships with industry counterparts, academia, and IT-security providers, sharing the same view to maintain continuous knowledge flow, treat risks, and conduct joint research (Boyens, 2022). The organization can formulate a unified front by contributing resources and expertise of the members, thereby generating a culture of information sharing and partnerships between the cyber security workforces.
Importance of Ongoing Monitoring, Evaluation, and Continuous Improvement
The requisite and ever-more needed ability of ongoing monitoring, evaluation, and continuous improvement in changing cyberattacks and technological advancement can’t be undervalued. A company like Cerious Cybernetics Corp must have robust processes that enable instantaneous monitoring of information systems, network traffic, and user activities that are anomalous or behave differently to spot security incidents quickly (O’Donnell and Gupta, 2023). Conducting periodic analyses of an organization’s data protection and risk management schemes for every service is very important, as well as reporting existing gaps in security status and new upcoming risks. The SC represents conducting regular audits, penetration tests, and tabletop exercises, which aim to stress-test the efficiency of the existing controls and response measures.
Besides that, Cerious Cognitive Corp. has to think about an education culture and how feedback is a part of this. It should involve security events, near-inconsequential events, and lessons learned. The system output should showcase weaknesses and avenues to improve policies, procedures, and technical controls. Through the above, this organization shall withstand these new challenges and threats. CyberSec Cybers could enforce proactive strategies by adapting to growing cyber threats and technological developments and emphasizing the necessity of ongoing monitoring, evaluation, and optimization (Boyens, 2022). Through such plans, CyberSec Cybers can strengthen its practice of information assurance and risk management as a way to protect its critical assets and their operations in highly unstable, so-called dynamic environments.
Summary/Conclusions
To sum up, the study conducted on Cerious Cybernetics Corp. revealed crucial information assurance and risk management mapping. The main conclusions underline the significance of implementing detailed policies, adequate procedures, and adequate practices considering the unique features and conditions of the organization’s culture and industry. Examining active cyber threats with a special focus on ransomware requires the organization to act beforehand, using secure network infrastructure and identity management systems and developing response protocols to capture incidents promptly.
As a result of these issues, the Cerious Cybernetics Corp. management should concentrate their efforts on cybersecurity initiatives that can remove the already discovered loopholes and the ones that are slowly evolving. This would also mean establishing and maintaining a comprehensive information security policy and regulations and regular staff training that will involve raising their awareness and engagement of strategic partners to foster collaboration and information sharing within the cybersecurity community. In addition, the whole monitoring, appraising, and improvement process is best defined for the organization to become fitter against any hidden threat and technology outputs. Through a dynamic strategy based on information security and risk management, Serious Cybernetics Corp. will be precluded from making any asset compromises and will also maintain legal compliance as a reliable pioneer in cybernetics R and D.
References
Ademola, E. (2021). Towards an Effective Information Assurance and Risk Management (IA&RM) Guide: A Case Study. Journal of Behavioural Informatics, Digital Humanities and Development Research, [online] 7(1), pp.45–56. doi: https://doi.org/10.22624/AIMS/BHI/V7N1P3.
Alshurideh, M., Alquqa, E., Alzoubi, H., Kurdi, B. and Hamadneh, S. (2023). The effect of information security on e-supply chain in the UAE logistics and distribution industry. Uncertain Supply Chain Management, [online] 11(1), pp.145–152. Available at: http://m.growingscience.com/beta/uscm/5833-the-effect-of-information-security-on-e-supply-chain-in-the-uae-logistics-and-distribution-industry.html.
Apirion, A. (2023). Council Post: Protecting Critical Infrastructure: Enhancing OT Security. [online] Forbes. Available at: https://www.forbes.com/sites/forbestechcouncil/2023/11/01/protecting-critical-infrastructure-enhancing-ot-security/ [Accessed 4 Apr. 2024].
Boyens, J.M. (2022). Cybersecurity Supply Chain Risk Management for Systems and Organizations. Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations. [online] doi: https://doi.org/10.6028/nist.sp.800-161r1.
Brunner, M., Sauerwein, C., Felderer, M. and Breu, R. (2020). Risk management practices in information security: Exploring the status quo in the DACH region. Computers & security, 92, p.101776. doi: https://doi.org/10.1016/j.cose.2020.101776.
Engelbrecht, H., Lindeman, R.W. and Hoermann, S. (2019). A SWOT Analysis of the Field of Virtual Reality for Firefighter Training. Frontiers in Robotics and AI, 6. doi: https://doi.org/10.3389/frobt.2019.00101.
Kandasamy, K., Srinivas, S., Achuthan, K. and Rangan, V.P. (2020). IoT cyber risk: a holistic analysis of cyber risk assessment frameworks, risk vectors, and risk ranking process. EURASIP Journal on Information Security, [online] 2020(1). doi: https://doi.org/10.1186/s13635-020-00111-0.
Mishra, A., Alzoubi, Y.I., Gill, A.Q. and Anwar, M.J. (2022). Cybersecurity Enterprises Policies: a Comparative Study. Sensors, [online] 22(2), p.538. Available at: https://www.ncbi.nlm.nih.gov/pmc/articles/PMC8778887/.
Nifakos, S., Chandramouli, K., Nikolaou, C.K., Papachristou, P., Koch, S., Panaousis, E. and Bonacina, S. (2021). Influence of Human Factors on Cyber Security within Healthcare Organisations: A Systematic Review. Sensors, [online] 21(15), p.5119. doi: https://doi.org/10.3390/s21155119.
O’Donnell, B. and Gupta, V. (2023). Continuous Quality Improvement. [online] PubMed. Available at: https://www.ncbi.nlm.nih.gov/books/NBK559239/.
Stoneburner, G., Goguen, A. and Feringa, A. (2022). Risk Management Guide for Information Technology Systems Recommendations of the National Institute of Standards and Technology. [online] Available at: https://www.hhs.gov/sites/default/files/ocr/privacy/hipaa/administrative/securityrule/nist800-30.pdf.
 write
write